Trusted devices: What are they?
Every device you that needs to sync with your iCloud vaults must be listed in the "Devices" section of the Secrets' settings. But why is this needed?
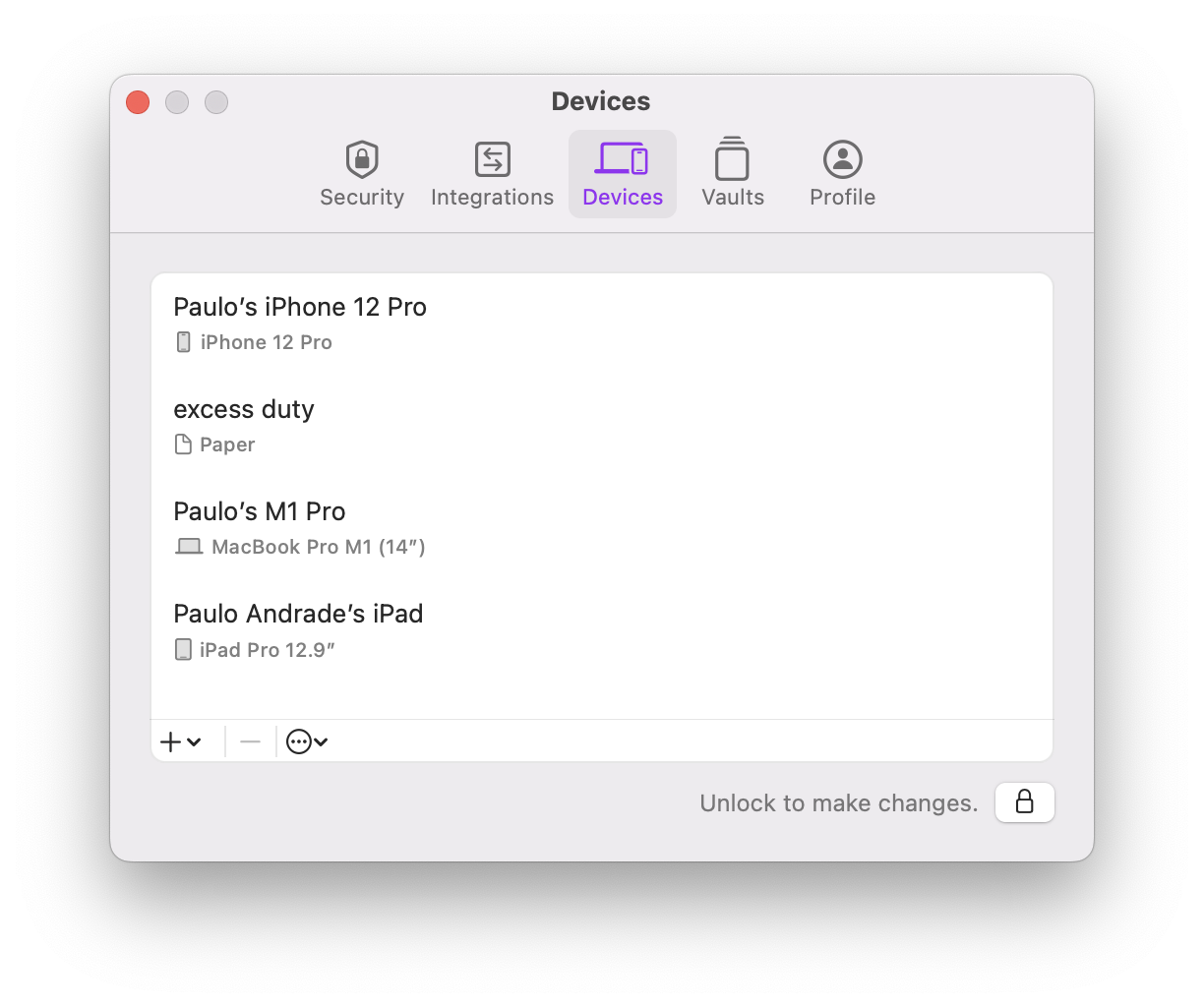
Example 'Devices' tab in Secrets's settings for macOS.
If you are using Secrets with more than one device, you've already had to go through an authorization step to add the new device. The reason why you need to do this is simple: trust.
Each of your devices needs to trust each other. Trusted devices can share secrets with each other, such as iCloud vault keys, and ultimately act on behalf of the user. This trust is established with public-key cryptography.
On the first run, each device will generate its own set of keys. During the authorization step, a new device will send its public-key to some trusted device and prove it owns the corresponding private key (the private key never leaves the device). The trusted device will then add this new device to the Device Trust Chain and share iCloud vault keys, allowing it to sync with those vaults1.
Device Trust Chain
The Device Trust Chain is a tamper-proof ledger that enables a secure record-keeping of every device that was authorized or revoked. Each link on this chain corresponds to either an authorization or a revocation of a device. The chain uses cryptographic primitives, such as hash functions and digital signatures, to ensure integrity, immutability, and trust[^bitcoin].
The previous paragraph may sound familiar if you've read about bitcoin. The trust chain does share similarities with the blockchain… but without the evironmental impact of mining.
You can learn more about trust chains and the Device Trust Chain specifically on our security design page. But it suffices to say that the devices you see listed in the "Devices" section above are your trusted devices, and that this list is tamper-proof. Meaning that nobody can go behind your back and add a device to that list without invalidating the trust chain.
Different Unlock Methods
In Secrets 3, you never had to authorize any new device... so why does Secrets 4 need this? The answer is: flexible authentication methods.
Previously, your passphrase was the key to your data on all of your devices, including iCloud. That meant you had to use the same pasphrase everywhere.
But different devices have different security risks. You desktop Mac at home is not as vulnerable as your iPhone that you carry with you all the time. Also, in Secrets 3, most people would just enable Touch ID or Face ID and never have to type their passphrase (leading to many forgetting it).
In Secrets 4 I wanted to acknowledge this and that's why it supports so many unlock methods. Including using just Touch ID or Face ID! You don't even have to setup a passphrase if you don't want to. And more importantly, each device can have its own unlock method.
Paper Devices
Finally, there's a special trusted device that's called a Paper Device. Paper devices can act just like any other trusted device, but they can also be used as recovery keys on all your trusted devices.
You may need to use a recovery key if you forget your passphrase, your Face ID sensor malfunctions, you have a burnt finger and can no longer use Touch ID, you need to restore from a backup, etc. So make sure you've created your paper device and have stored the printed page somewhere safe.
